Use this guide to configure Okta as the identity provider for CodeRabbit. The current setup is support-assisted: you create the Okta SAML application, collect the required metadata, and then send the final values to CodeRabbit for enablement.Documentation Index
Fetch the complete documentation index at: https://docs.coderabbit.ai/llms.txt
Use this file to discover all available pages before exploring further.
Before you start
Make sure you have:- Access to the Okta Admin Console
- The email domain that should authenticate through CodeRabbit
- A way to reach your account team to request CodeRabbit’s service provider values and submit your final metadata
What CodeRabbit provides
Before you configure the Okta app, reach out to your account team to request these values:- Single sign-on URL (ACS URL)
- Audience URI (SP Entity ID)
What CodeRabbit needs from you
After you create the Okta app, send these four items to CodeRabbit:- Email domain: for example,
yourcompany.com - Sign-on URL: the IdP Single Sign-On URL from Okta metadata
- Issuer: the IdP issuer or entity ID from Okta metadata
- Signing certificate: an X.509 certificate file in
.pemor.cerformat
Set up the Okta app
Create the Okta app integration
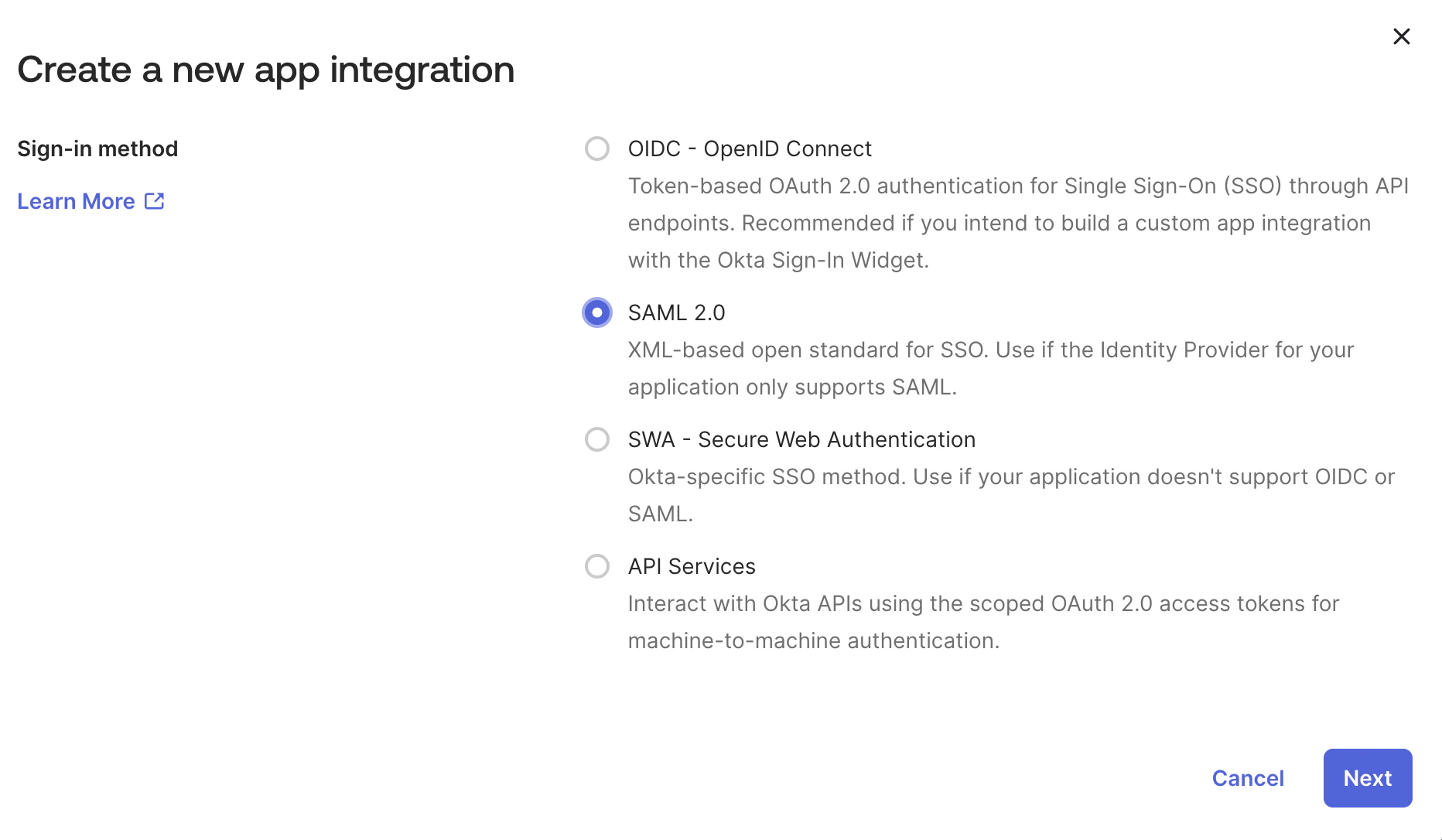
Sign in to your Okta Admin Console, then go to Applications -> Applications and click Create App Integration.In the Create a new app integration dialog, select SAML 2.0 and click Next.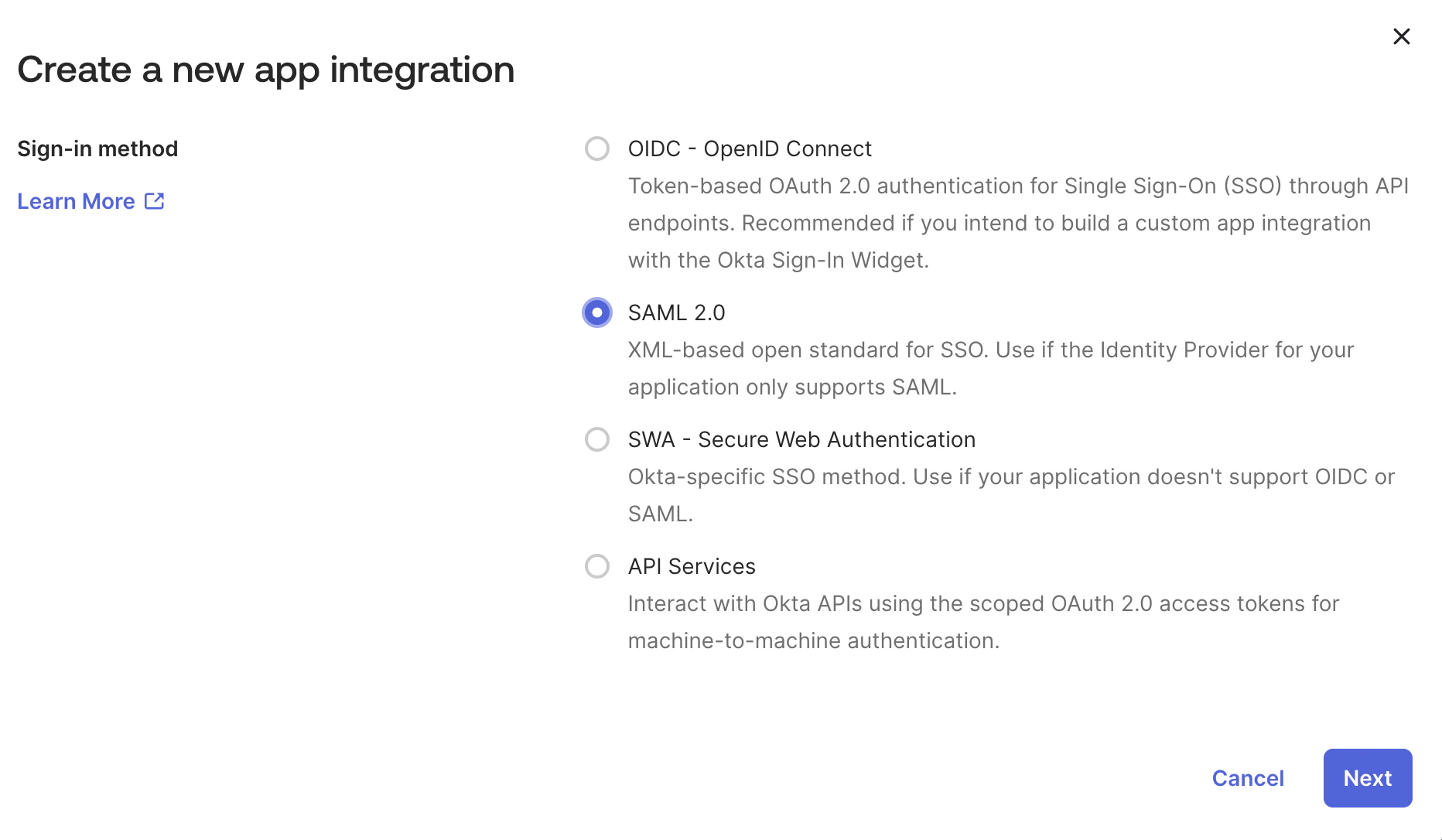
CodeRabbit, optionally upload a logo, and continue to the SAML configuration screen.Fill in the SAML configuration
In the SAML settings screen, use the following values:
No attribute statements are required. Leave the Attribute Statements and Group Attribute Statements sections empty.Click Next and complete the wizard to create the application.
| Field | Value |
|---|---|
| Single sign-on URL | Provided by CodeRabbit |
| Audience URI (SP Entity ID) | Provided by CodeRabbit |
| Default RelayState | Leave blank |
| Name ID format | EmailAddress |
| Application username |
Retrieve your Okta SAML metadata
After the app is created, open Applications -> Applications -> your CodeRabbit app -> Sign On.Scroll to SAML Signing Certificates, find the certificate marked Active, and open Actions -> View IdP metadata. This opens the XML metadata page that contains the values CodeRabbit needs.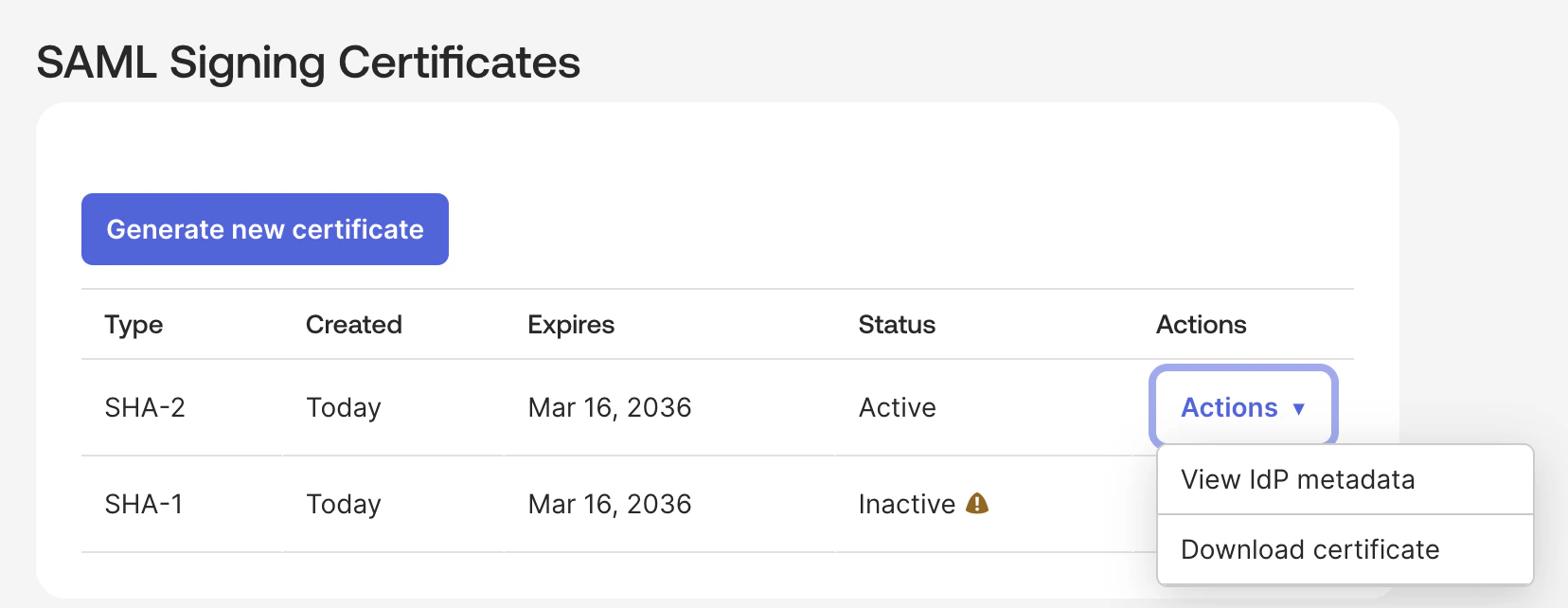
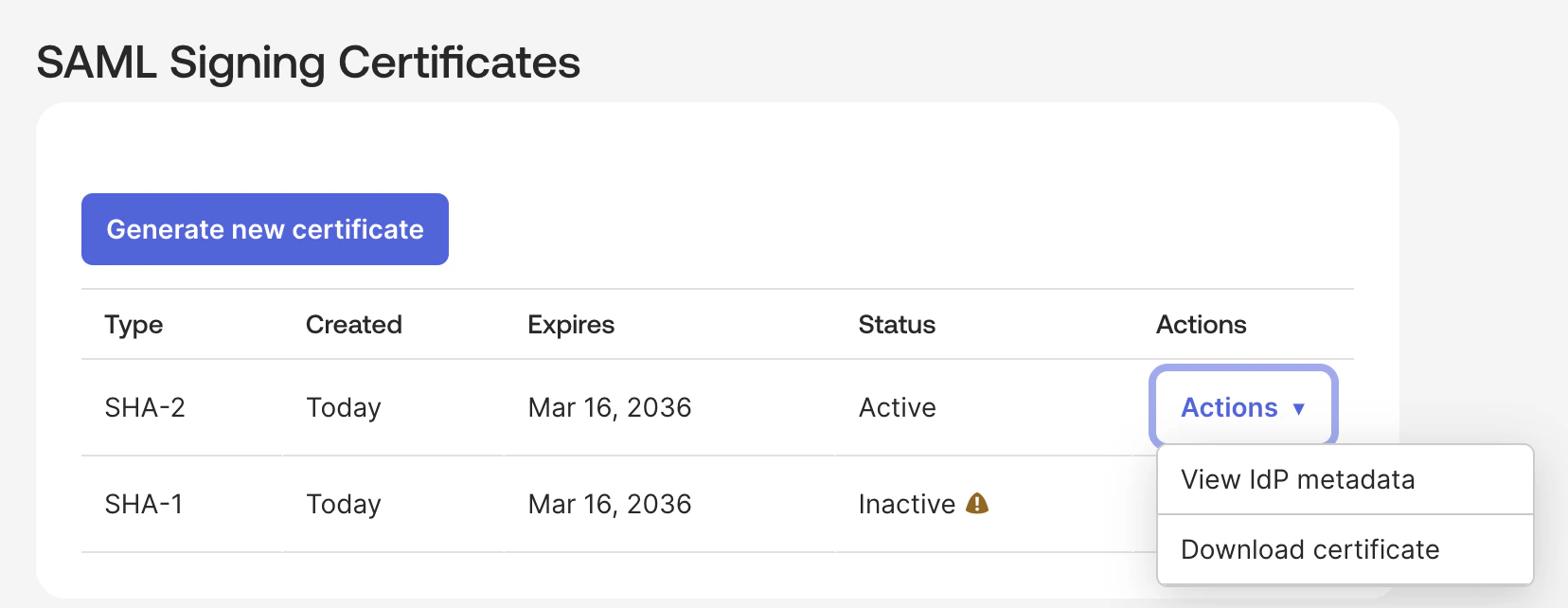
- Sign-on URL: copy the
Locationattribute from themd:SingleSignOnServiceelement - Issuer: copy the
entityIDattribute from themd:EntityDescriptorelement - Signing certificate: copy the
ds:X509Certificatevalue
.pem format:Assign people or groups
Open the Assignments tab for the app, click Assign, and assign the people or groups that should be allowed to sign in to CodeRabbit.Users cannot authenticate through Okta until they are assigned to the application.
Send the configuration to CodeRabbit and validate access
Send the following items to your account team:
- Your organization’s email domain
- The Okta Sign-on URL
- The Okta issuer
- The signing certificate file
What’s next
Enterprise SSO overview
Return to the SSO overview to see the shared rollout flow and future provider coverage.
Roles and permissions
Pair SSO with the right access controls by reviewing how roles work in your CodeRabbit organization.
Support
Reach out if you need the CodeRabbit service provider values or help troubleshooting the Okta setup.