| The CodeRabbit Reverse Tunnel is a private-network connectivity option for Enterprise customers who cannot expose their Git platform to the public internet. A CodeRabbit-provided Connector runs inside your network, dials out to CodeRabbit over WebSocket Secure (WSS), and carries CodeRabbit-initiated API and HTTPS Git traffic through that existing outbound session.Documentation Index
Fetch the complete documentation index at: https://docs.coderabbit.ai/llms.txt
Use this file to discover all available pages before exploring further.
Intended use
The CodeRabbit Reverse Tunnel is intended for Enterprise customers with the constraints defined below:- GHES runs in a private subnet, private cloud account, or on-premises network.
- GHES cannot receive inbound connections from CodeRabbit or the public internet.
- Your security policy does not allow inbound firewall exceptions, vendor IP allowlisting on the GHES side, or external PrivateLink peering.
For GHES instances that CodeRabbit can already reach directly, use the standard GitHub Enterprise Server guide.
Components
The CodeRabbit Reverse Tunnel has four components:- Reverse Tunnel Gateway — A CodeRabbit-managed edge service that accepts Connector sessions and exposes tenant-scoped HTTPS routes for CodeRabbit services to call into.
- Reverse Tunnel Connector — A lightweight, CodeRabbit-provided container that runs inside your network and establishes a long-lived outbound connection (WSS over HTTPS) to the Reverse Tunnel Gateway. CodeRabbit then sends runtime requests — clone, read pull requests, post review comments — over this pre-established tunnel. The Connector dials out from your network; no inbound ports are opened.
- Route key — A unique, opaque routing identifier issued by CodeRabbit for your tenant. CodeRabbit uses the route key to direct runtime traffic to the correct Connector session, so your private GHES address is never exposed in the URL path.
- Connector token — A bearer token issued by CodeRabbit for your GHES tenant. Multiple Connector replicas can share the same token.
Architecture

| Direction | Purpose | Network path |
|---|---|---|
| Inbound (CodeRabbit → GHES) | Clone repositories over HTTPS, read pull requests, fetch files and commits, create reviews, post comments, and update checks | CodeRabbit services call the Reverse Tunnel Gateway, which forwards the request into your network over the long-lived WSS session opened by the Reverse Tunnel Connector. The Connector then makes an internal call to GHES. |
| Outbound (GHES → CodeRabbit) | Deliver webhook events such as pull request opened, synchronized, reviewed, or commented | GHES sends standard HTTPS webhooks outbound through the customer NAT gateway to the CodeRabbit webhook receiver. |
PR review flow through the Tunnel
End-to-end view of how a single pull request moves through the CodeRabbit Reverse Tunnel. None of the network mechanics are visible to the developer — from their point of view, CodeRabbit simply reviews their PR.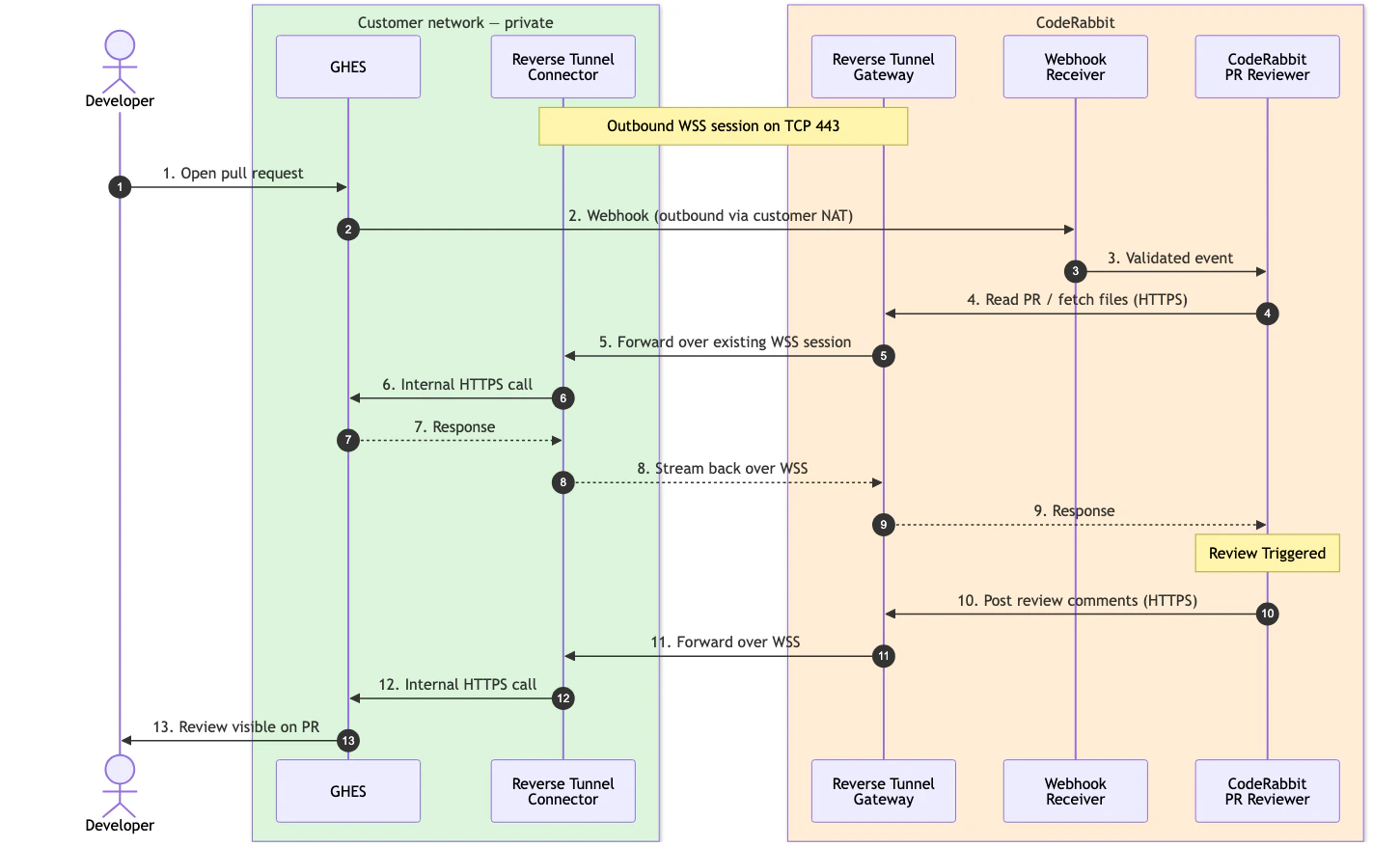
- Developer opens a PR inside your private GHES.
- GHES sends a webhook to CodeRabbit outbound through your customer NAT, signed with your GitHub App webhook secret.
- CodeRabbit reads the PR through the tunnel. The Reverse Tunnel Gateway routes the request over the existing WSS session; the Reverse Tunnel Connector forwards it to GHES and streams the response back.
- CodeRabbit runs the review and writes the feedback.
- CodeRabbit posts the comments back through the same tunnel, and the review appears on the pull request in GHES.
High availability
Run at least two connector replicas for production. All replicas for the same GHES tenant normally share the same gateway URL, connector token, route key, target base URL, and origin TLS policy. The gateway tracks the live connector sessions for the route and uses an active session for each new request. Important behavior:- New requests can use another live connector after a connector disconnects.
- In-flight requests are not transparently moved to another connector.
- The connector reconnects automatically with exponential backoff after a lost WSS session.
Capacity and limitations
The tunnel streams request and response bodies with backpressure, so it supports large HTTPS clone/fetch traffic. Capacity is still bounded by your connector replicas, network egress, and GHES origin capacity.| Area | Behavior |
|---|---|
| Concurrency | The gateway enforces a per-connector concurrent stream limit. CodeRabbit provides the active limit during onboarding. Add connector replicas to increase available concurrency. |
| Buffering | The connector does not provide durable buffering while offline. If a connector is down, new GHES runtime calls fail until another connector is available. |
| Git protocol | HTTPS only. |
| Platform support | Currently available for GitHub Enterprise Server only. For information about support for GitLab, Azure DevOps, and other Git platforms please contact CodeRabbit Sales team. |
FAQ
Does CodeRabbit need inbound access to our network?
Does CodeRabbit need inbound access to our network?
No. The connector opens an outbound WSS session to CodeRabbit. CodeRabbit-initiated GHES traffic rides over that existing session.
Can we run multiple connector pods?
Can we run multiple connector pods?
Yes. Multiple connector replicas can serve the same route key. Give each live replica a unique
REVERSE_TUNNEL_CONNECTOR_ID.Can we restrict outbound destinations?
Can we restrict outbound destinations?
Yes. The connector needs outbound HTTPS to the CodeRabbit gateway and HTTPS reachability to your GHES origin. GHES needs outbound HTTPS to the CodeRabbit webhook receiver.
What happens if the tunnel drops during a review?
What happens if the tunnel drops during a review?
The connector reconnects automatically. In-flight requests fail and are retried only when CodeRabbit can safely retry the operation.
Can this forward other internal services?
Can this forward other internal services?
No. The tunnel is scoped to GHES HTTP(S) and HTTPS Git traffic for CodeRabbit. It is not a general-purpose private-network proxy.
What’s next
GitHub Enterprise Server setup
Create the OAuth App, GitHub App, webhook secret, and permissions used by the GHES integration.
Platform overview
Review all supported Git platforms and choose the right integration path for your environment.
Support
Contact CodeRabbit for reverse-tunnel onboarding, connector credentials, and deployment guidance.